Trust center
OT/IT separated by architecture. Not by promise.
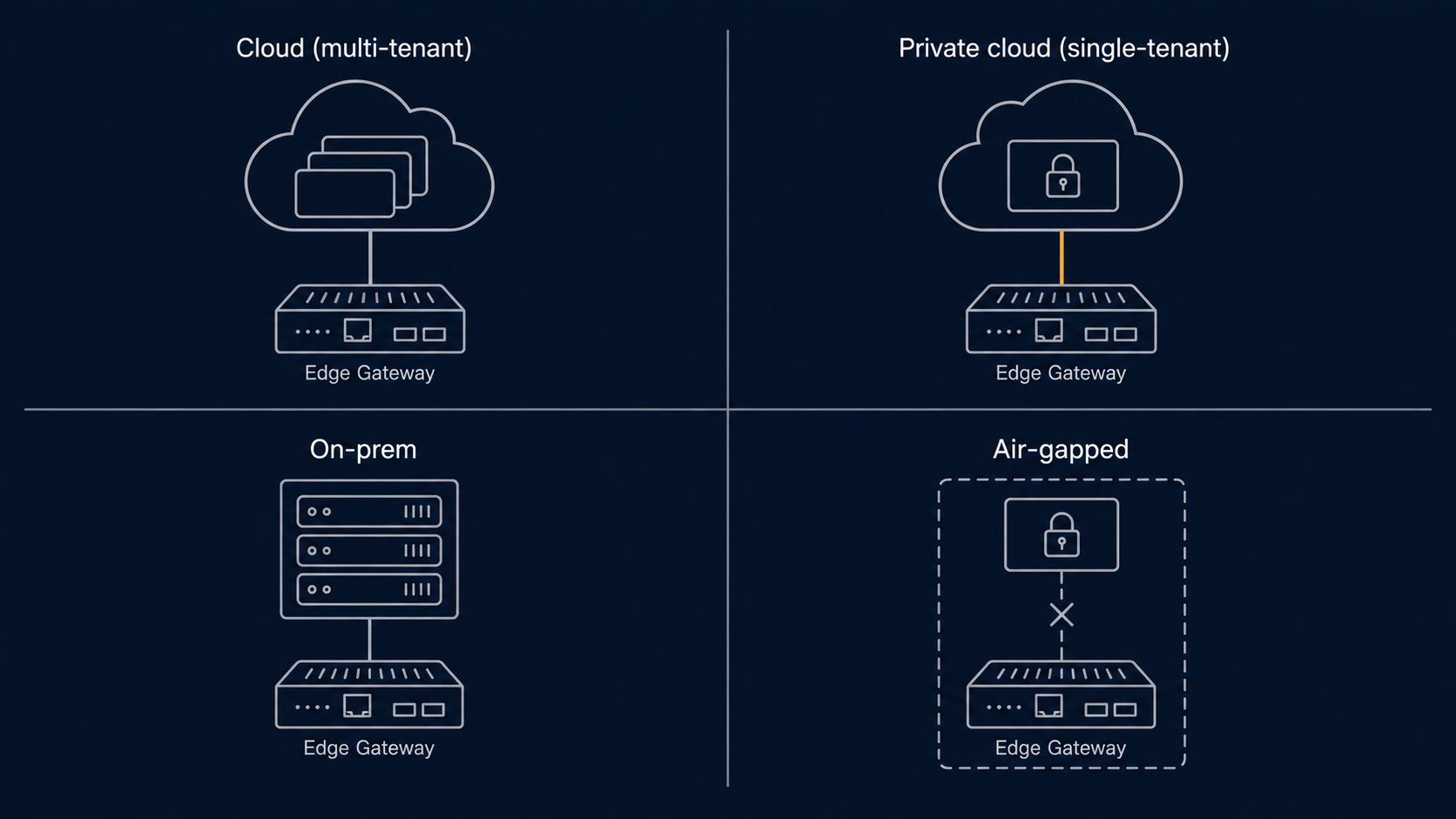
The boundary that protects the asset is built into the LumeTrax® architecture, not promised in a sales call. Trust roadmap dated and public. Data neutrality contractual. Cloud, private, on-prem, or air-gapped — same software, four deployment shapes.
Soft gate — email optional. The pack covers architecture, deployment topology, identity, data residency, sub-processors, incident handling, responsible disclosure, and pre-completed common-framework questionnaires.
Mission-critical control never moves out of the deterministic SCADA boundary. Always.
Renewable assets sit on infrastructure that has to fail safely. Supervisory control, interlocks, and safety-critical command sequencing are the responsibility of the OT layer — SCADA, PLC, RTU, on-site controller — where determinism is provable and the failure mode is engineered, not negotiated.
Analytics, workflow, optimization, and assurance run above that boundary, in shared platform services. Useful, valuable, increasingly intelligent — but never the layer protecting the asset.
The boundary is drawn into the architecture as a first-order constraint, not a sales-deck slide. Adding a feature on the platform side never compromises the deterministic side. New OEM ecosystems are added inside ingestion, not inside control. Network segmentation is real, audited, and enforced — not asserted.
Sequenced by what enterprise procurement actually asks for. Not by badge collection.
Transparent, current, and updated as each step closes.
Status updates land on this page as the work moves. We don't claim a certification we don't hold. We don't bury status changes in a footer. Procurement teams that ask for current attestations get them in a business day.
- Internal secure SDLC aligned to IEC 62443-4-1In implementation
- ISO 27001 (ISMS)In preparation
- ISO 9001 (QMS)In preparation
- Third-party penetration testingScheduled
- Customer security pack publishedIn preparation
- SOC 2 Type IIOn the roadmap
- ISO 22301 (business continuity)On the roadmap
- Project-specific DNV / TÜV / SGS assessmentsAvailable on request
Status legend: In implementation = active build · In preparation = scoping and gap assessment underway · Scheduled = on the calendar with a named provider · On the roadmap = committed direction, sequenced after the foundation closes · Available on request = engagement-specific assurance work, scoped per project.
Regional readiness for North American market deployments
NERC CIP alignment available on request.
For deployments in the North American electricity market, NERC CIP alignment is available on request as part of the engagement scope. We don't carry a blanket NERC CIP attestation — the regulation applies to specific asset thresholds and operating contexts, and the right scope is determined per deployment. Customers operating bulk-electric-system assets that fall under NERC CIP can request the alignment package as part of the Core questionnaire.
Concrete commitments, not soft governance
Customer data belongs to the customer. Committed in the website and in the contract.
The seven commitments below are published policy on this page. They also appear verbatim in the customer DPA / MSA — they're contractual, not aspirational. Independence isn't a marketing claim; it's a documented policy that customers can audit and require in writing.
The seven commitments.
- 01Customer data belongs to the customer.
- 02Tenant data is segregated by architecture.
- 03LumeTrax does not share plant-level data with OEMs, EPCs, O&M contractors, lenders, or affiliates unless explicitly authorised by the customer in writing.
- 04Cross-portfolio benchmarking is opt-in and anonymised.
- 05Commercial teams do not access customer operating data except for contracted support, audit, or advisory scope.
- 06LumeTrax does not resell or license customer operating data to any third party.
- 07Where LumeTrax software is installed, Audit & Assurance reports distinguish measured data, calculated outputs, assumptions, and reviewer judgment — sources are not blended.
Cloud, private, on-prem, or air-gapped. Same software, four shapes.
Cloud (multi-tenant)
Default deployment. Shared platform services on a managed cloud region.
When to use: Most asset owners and operators. Fastest to deploy, fastest to update.
Private cloud (single-tenant)
Isolated cloud deployment per customer organisation. Same operations team, separate data and infrastructure.
When to use: Customers with internal security policies that require single-tenancy or specific cloud-region pinning.
On-prem
Customer-controlled deployment in customer or partner datacentre.
When to use: Regulators or contracts requiring data and compute under customer control.
Air-gapped
On-prem with no inbound or outbound platform connectivity.
When to use: Restricted-network or sovereign-control projects. Ingestion and operations work entirely inside the customer perimeter.
The deployment shape is decided in the Core questionnaire. Subsequent shape changes (e.g. cloud → private) are supported as commercial requirements evolve.
Who can do what — provable, not asserted
Enterprise identity. Scoped roles. Full audit trail.
Single sign-on
Multi-factor authentication
Role-based access + audit log
Encryption + tenant isolation
- In transit: TLS 1.3 minimum for all platform endpoints; mTLS for edge-gateway-to-cloud sync where deployment shape supports it
- At rest: AES-256 for historian, configuration, document storage; per-tenant encryption keys; key rotation cadence documented in the security pack
- Tenant isolation: Logical isolation in multi-tenant cloud (per-tenant DB schemas + row-level security); physical isolation in private-cloud and on-prem deployments
- Network segmentation: OT/IT boundary enforced at network layer in addition to architecture layer; explicit allow-lists for cross-boundary flows
Where data lives, and who can reach it
Operating data stays where the contract says it stays.
Cloud and private-cloud deployments are pinned to specified regions at engagement (typically EU, MEA, or customer-requested). On-prem and air-gapped deployments don't leave the customer perimeter. Sub-processors with any operating-data access are listed in the customer security pack and updated as the list changes — customer notice provided ahead of additions, with the right to object built into the contract.
Documented RPO and RTO targets per deployment shape.
Backup cadence
Recovery point objective (RPO)
Recovery time objective (RTO)
Notification timing, content, and escalation defined contractually.
- Customer notification: typically a 24-hour first-notification target for incidents affecting the customer's tenant; defined contractually per engagement
- Escalation path: documented per deployment, including customer security contact, LumeTrax incident commander, and any required regulatory or insurance notifications
- Postmortems: shared on a defined cadence, with customer review of factual accuracy before publication
- Coordinated disclosure: for vulnerabilities affecting multiple customers — see Responsible Disclosure below
If you've found something, tell us.
Vulnerability reports go to security@lumetrax.com (routed to info@lumetrax.com until the dedicated alias is provisioned). We acknowledge within 2 business days, triage within 5, and target a remediation timeline proportionate to severity. Coordinated disclosure is preferred. Researchers acting in good faith won't be threatened with legal action.
A formal bug-bounty programme is on the roadmap; pre-launch reporters can request acknowledgement in published security advisories.
CAIQ, SIG, custom — pre-completed where standardised.
The customer security pack pre-completes the most common framework questionnaires (Cloud Security Alliance CAIQ, Shared Assessments SIG) so procurement teams don't run a 200-question manual completion exercise. For customer-specific questionnaires, the LumeTrax Engineering team handles bespoke responses inline — typical turnaround 5 business days for a full custom questionnaire, 1–2 days for incremental clarifications.
One PDF. Procurement-grade detail.
The customer security pack collects the documentation enterprise procurement and lender IE teams routinely ask for, in one structured document.
Frequently asked questions
- Cloud and private-cloud deployments are pinned to a specified region at engagement (typically EU, MEA, or customer-requested). On-prem and air-gapped deployments don't leave the customer perimeter. Region map is in the security pack.
- SOC 2 Type II is on the roadmap. Status is updated on this page as it changes. Customers needing equivalent assurance pre-completion can request the current ISO 27001 status, the most recent third-party pen-test letter, and the architecture overview from the security pack.
- SAML 2.0 and OIDC are supported. Most enterprise IdPs (Okta, Entra, Google Workspace, Ping, ADFS) configure cleanly during standard onboarding. Customer-specific configuration is part of standard onboarding.
- Yes — the security pack pre-answers the most common framework questionnaires, and the Engineering team handles bespoke questionnaires inline. Typical turnaround on a custom questionnaire is 5 business days.
- Incident response playbook is in the security pack. Customer notification timing, content, and escalation path are defined contractually — typically a 24-hour first-notification target for incidents affecting the customer's tenant. Postmortems shared on a defined cadence.
- Yes. Both are first-class deployment shapes — not bolt-ons. Sized in the Core questionnaire.
- NERC CIP alignment is available on request as part of the engagement scope. The right scope depends on the asset's specific NERC CIP applicability and the operating context — confirmed in the questionnaire.
- Not yet. Coordinated disclosure to security@lumetrax.com is the current path. Acknowledgement and remediation policy described above. A formal programme is on the roadmap.
- See the Data Neutrality section. Seven commitments published on this page and contractual in the customer DPA / MSA. Short version: customer data belongs to the customer, no third-party sharing without written authorisation, no commercial use beyond contracted scope, no resale.
Security shapes the platform — read about it on the platform and product pages too.